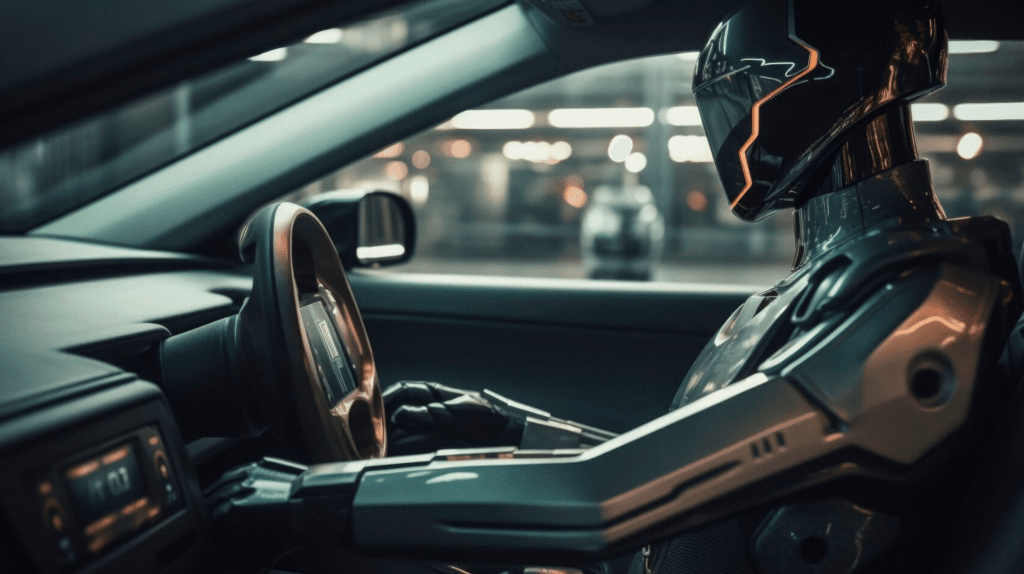
The automotive and mobility industries are experiencing a significant surge in cyberattacks, with incidents becoming more frequent and severe. In 2024, approximately 60% of cybersecurity incidents in these sectors affected “thousands to millions” of assets, including vehicles, charging stations, smart mobility apps, and connected devices.
Key Factors Contributing to the Rise in Cyberattacks:
- Increased Connectivity: The proliferation of software-defined vehicles and electric vehicle (EV) charging stations has expanded the attack surface, providing more entry points for malicious actors.
- Advanced Threats: Cybercriminals are leveraging generative AI to automate complex phishing attacks and develop sophisticated malware capable of evading traditional detection systems.
- High-Value Targets: Automotive dealerships and manufacturers are attractive to cybercriminals due to the vast amounts of personally identifiable information (PII) they handle. In 2024, the automotive industry witnessed a 225% increase in cyberattacks over the past three years, with remote attacks accounting for 85% of incidents.
Notable Incidents:
- Legal Disputes Over Data Breaches: In February 2025, CDK Global, a prominent automotive retail software provider, filed a lawsuit against rival Tekion, alleging an illegal hacking campaign aimed at stealing confidential data from dealership computer systems.
- Vulnerabilities in Connected Vehicles: Researchers discovered a vulnerability in Kia’s web portal that allowed hackers to remotely access and control modern internet-connected vehicles using only the car’s license plate number. This flaw enabled unauthorized unlocking of cars, tracking of locations, and operation of various features.
Implications and Recommendations:
The escalation of cyber threats in the automotive and mobility sectors underscores the urgent need for robust cybersecurity measures. Organizations are advised to implement comprehensive security strategies, including:
- Adopting Zero-Trust Architectures: Ensuring that all users, both inside and outside the organization, are authenticated and continuously validated.
- Enhancing Employee Training: Educating staff about social engineering attacks, such as phishing, to reduce human error, which accounts for a significant portion of security breaches.
- Securing Supply Chains: Addressing vulnerabilities in third-party software and hardware components to prevent supply chain attacks.
As vehicles become increasingly connected and reliant on software, the importance of cybersecurity in protecting consumer data and ensuring safety cannot be overstated.